vRealize Automation 6.1 (formally vCAC) – Identity Appliance High Availability & Backup
In a previous post, we discussed the importance of SSO as it relates to vRA (vRealize Automation). We also demonstrated how to deploy & configure the vRA identity appliance. Due to the nature of the identity appliance we need to make sure that SSO is in a high available state. There currently is no native HA feature built in, so what are our options for protecting the identity appliance you ask? Here are some options:
- The first option is leveraging vSphere HA, which is the recommend method.
- The use of FT (Fault Torrance) could be another method; the identity appliance is within the one vCPU boundary.
- Deploy the vSphere windows SSO in an HA pair. Some things to keep in mind:
- Certificates – like it, love it, gotta have it!
- vCenter SSO 5.5 U2, U2a, or U2b are supported with vRA 6.1. Although SSO 5.5 U2b is the recommendation.
- External load balancer (F5 documented).
How to configure SSO for high availability with vRA 6.1 can be found here.
Backups Save Lives!
Does having high availability guarantee 99% up time? How often do we design with HA in mind? Yet gremlins, not ones in the movies but the datacenter kind, can cause the unexpected. Better yet are we protected from ourselves, meaning human error? These questions and concerns lead to making sure there is some sort of “plan B”. Backups provide a plan that minimizes your downtime and saves your bacon, yes I said it! SSO is a critical component of any vRA deployment, regular scheduled backups of the should be in place. Especially when changes to configuration, tenants and identity store(s) occur. Here are a few methods to backing up the identity appliance (SSO):
- vSphere Data Protection – creates a backups of the entire appliance.
- vSphere Replication – replicate the virtual appliance to another site.
- Site Recovery Manager – shadow VM copy of the appliance in another datacenter.
- Cloning / Snapshot – a lot of up keep here, use as temporary solution only.
- 3rd party backup solutions.
Backup of Identity Appliance SSO database using vdcbackup
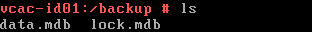
- Log in identity appliance console.
- Create a backup directory “mkdir /backup“.
- Run the following command “/usr/lib/vmware-vmdir/bin/vdcbackup (space) /storage/db/vmware-vmdir /backup/“.
- Verify the following files (data.mdb & lock.mdb)are in the backup directory “/backup”.
Note: Copy the cert located in “/etc/vmware-sso/keys” , copy files offline using a tool such as WinSCP.
*Bonus: Some Troubleshooting Tips*
- VMware Knowledge base is your best friend, most of the errors related to SSO can be found in a knowledge base search.
- Know where your logs are located:
- Identity appliance -Admin tab –> Logs allows creation of support bundle or see KB 2074803.
- vSphere SSO – %Temp% in windows explorer , see KB 2033430.
- Verify NTP is configured and synced correctly.
- If possible use certificates from a certificate authority.
- Use vdcadmintool to unlock and reset SSO administrator password.
- SSO administrator password in identity appliance has an expiration date (Admin tab –> Administrator settings). Only current option is change password.
- SSO password in vSphere expires in 90 days by default, password policies can be adjusted.
Thanks to Kyle Ruddy for his input towards SSO troubleshooting. With SSO highly available and backed up, we can now set our sites on deploying the vCAC appliance.